The Missing Piece in Your Microsoft 365 Contractor Migration
Verify the laptop before a contractor reaches Microsoft 365.
No MDM. No VDI. From $3 per user / month.
1.4M+ contractor devices verified at regulated enterprises.
Trusted by






What Ensure makes possible
One agent. Three jobs: verify the device, enforce the policy, log the evidence.
89%
lower contractor access cost
Verify contractor devices before Microsoft 365 access
Ensure checks the device at sign-in and tells your access policy whether to let it through.
1‑Click
audit export
Enforce device posture at the point of access
Every check is timestamped: who, what device, which controls, pass or fail. Export when audit asks.
< 5 min
average setup time
Onboard contractors fast without help desk overhead
Contractors install in minutes and fix most issues themselves. No help-desk ticket.
Your situation
Which problem are you solving?
Migration Owner
I'm trying to get contractors off VDI
Contractors are still stuck on VDI because their devices are unmanaged. See how to move them into Microsoft 365 and Windows 365 without lowering security.
CISO / Security Architect
I need proof contractor devices meet policy
Your team needs evidence that unmanaged devices meet security requirements at the moment of access. See what Ensure verifies, logs, and exports.
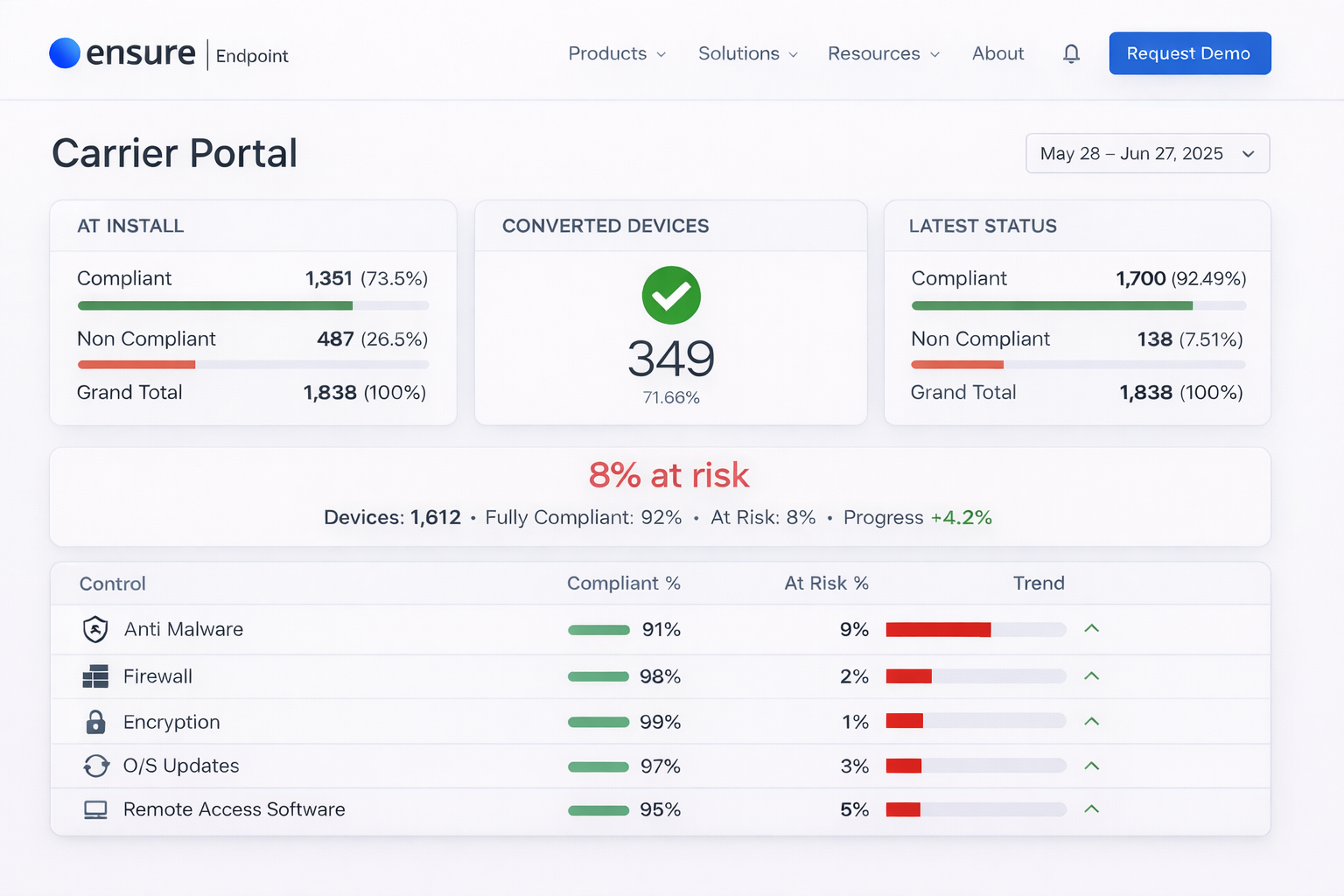
In production
How a regulated enterprise moved 2,000+ contractors off VDI and into Microsoft 365
Including partners from Accenture, Deloitte, and other global service providers.
Three steps
How Ensure verifies devices before Microsoft 365 access
Contractors attempt access, device posture is checked, and compliance evidence is logged automatically.
Contractor attempts to access Microsoft 365
Two lines of code on your portal trigger the check at sign-in. No new login screen.
Device posture is verified in seconds
Encryption, antivirus, firewall, OS patch, screen lock. Fail any check and the contractor gets guided steps to fix it.
Compliance evidence is logged automatically
Each check writes a timestamped record. Export anytime.
Why not just...
Every alternative breaks somewhere.
| Alternative | Where it breaks |
|---|---|
| Keep VDI for contractors | Defeats the migration. You keep paying for VDI after rolling out Microsoft 365. |
| Web-only access restrictions | Creates a degraded experience, breaks common workflows, and pushes contractors into workarounds. |
| Issue managed devices | Too expensive and too slow for large, rotating contractor populations. |
| Enterprise browser (Island, Talon) | Higher cost, browser change required, and more product than most teams need for basic device posture. |
| Accept the risk | Security won't sign off. Audit won't accept the gap. |
| Ensure Endpoint | $3/user/month. No MDM enrollment. Entra Conditional Access integration. Audit evidence. Live in days. |
Keep VDI for contractors
Defeats the migration. You keep paying for VDI after rolling out Microsoft 365.
Web-only access restrictions
Creates a degraded experience, breaks common workflows, and pushes contractors into workarounds.
Issue managed devices
Too expensive and too slow for large, rotating contractor populations.
Enterprise browser (Island, Talon)
Higher cost, browser change required, and more product than most teams need for basic device posture.
Accept the risk
Security won't sign off. Audit won't accept the gap.
Ensure Endpoint
$3/user/month. No MDM enrollment. Entra Conditional Access integration. Audit evidence. Live in days.
Ready to see it live?
See the contractor login, device check, and audit record live
Watch the full flow in 15 minutes: unmanaged device, posture check, access decision, guided remediation, and compliance record, without a slide deck.
Not ready to talk yet? Start here.
For IT & Security
VDI Migration Architecture Guide
How to verify contractor devices for Microsoft 365 access and retire VDI. Includes Entra Conditional Access architecture, deployment timeline, and compliance mapping.
For Operations & Finance
ROI Calculator
Enter your contractor count and current VDI cost to see annual savings, cost per user, and payback period.